Purdue researchers uncover vulnerabilities in Smart TVs
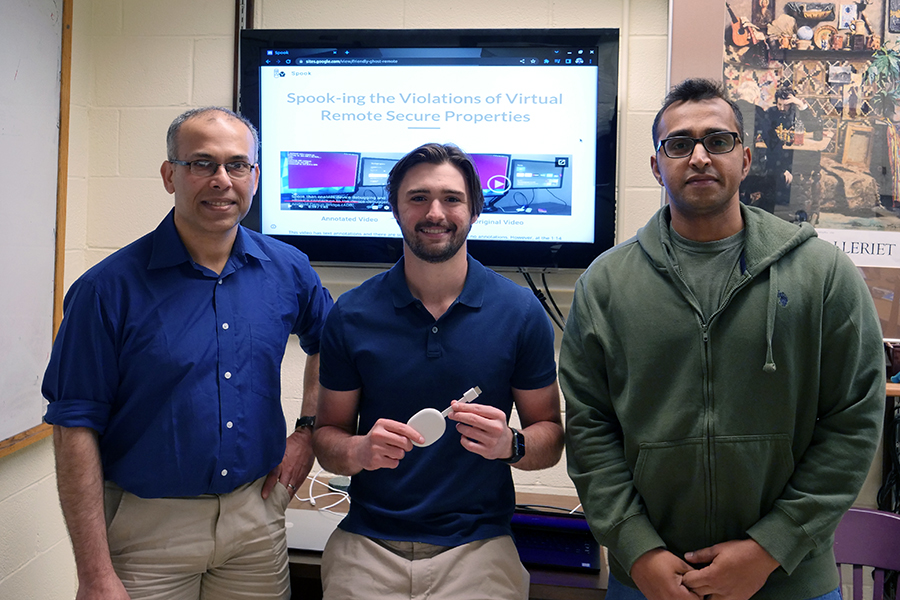
Purdue University researchers have discovered vulnerabilities in Smart TVs that can allow an attacker to control them and capture any data stored on them. The vulnerability has been acknowledged (CVE-2021-0889) by Google for their Android TV platform and they have made modifications to it to address this finding. The Purdue team comprises Saurabh Bagchi and Aravind Machiry, both faculty members in the Elmore Family School of Electrical and Computer Engineering, students Joshua Majors and Darren Wu, and Research Scientists Dr. Amiya Maji and Edgardo Barsallo.
Saurabh Bagchi, professor of electrical and computer engineering and computer science (by courtesy) at Purdue, and his team over the last five years have developed technology to understand the security of smart Internet of Things (IoT) devices. This most recent work has been accepted to the 18th ACM ASIA Conference on Computer and Communications Security (ASIACCS), where it was one of 16% of the submissions that were accepted.
“Before our work, it was not known that the protocol through which a phone acts as a remote for the TV has this vulnerability that can be used to totally take over the TV,” Saurabh said. “It was a big step forward that we could uncover the vulnerability through reverse engineering the remote protocol, and also suggest software changes to plug the vulnerability.”
Aravind Machiry, co-investigator on the project said, “In addition to finding a vulnerability, our work defines the security properties of virtual remote devices, enabling the secure development of future devices.”
Yingying Chen, professor and department chair of Electrical and Computer Engineering at Rutgers University is an expert in mobile security and was not affiliated with the study. She commented, “This kind of rigorous academic work is supremely important as we are increasingly embracing smart devices in our personal and our work lives. Studies like this help us first understand the new vulnerabilities that arise and the systematic ways to address them.”
There has been recent explosive growth of Over The Top (OTT) digital streaming platforms, reaching globally $101B in 2020 and expected to grow at a CAGR of 14% over the next 5 years. In the US itself, in 2020 a household on average has 1.64 OTT subscriptions. The OTT platforms are dominated by the manufacturers Roku, Apple, Amazon, and Google.
With the recent growth of these OTT platforms, purchases through streaming devices, especially Smart TVs, has also been growing rapidly, at a CAGR of 19.8% and is expected to reach $340.8B in 2027. Specifically, Android TV, developed by Google, has grown incredibly fast, doubling the number of devices each year since 2016. Currently, there are over 80M Android TV (and its newer variant Google TV) devices and more than 5K apps published in the Google Play Store for this platform. Smart TV devices store passwords to many different services a user may have, such as Google, Amazon Prime, and Netflix.
This makes them a ripe target for attacks meant for credential stealing or for using them as agents in a botnet. In August 2019 WootCloud disclosed a vulnerability in Android TV devices that allowed them to be employed in a botnet. A group of Princeton researchers showed the prevalence on OTTdevices of pervasive tracking and collecting device identifiers, while another study shows how to take over a smart TV running Android TV OS by abusing the infrared communication protocol when an attacker has direct access to the device. There have been a series of warnings and published exploits about smart TVs and set-top boxes, including some from government sources like the FBI.
Despite this sense that OTTs provide an attractive attack surface, there was little evaluation of the security architectures and the resulting foundational vulnerabilities of these streaming platforms. The work done by the research team uncovered the vulnerability in the WiFi remote protocol and showed that this attack targets four of the most popular OTT platforms. To translate this to practice, the team developed and showed the feasibility of Spook, a piece of malware packaged in an Android smartphone to take over an Android TV device.
The team designed and implemented a defense using ARM TrustZone, that guarantees that a human is initiating the pairing. This defense thwarts Spook as well as any UI injection-based attack against Smart TVs, providing a secure version of WiFi remote protocol. This does not increase the time that a user needs to interact with the TV in any noticeable way. Google acknowledged their findings as a security vulnerability, assigned it a CVE (an official nation-wide system used to track vulnerabilities in software and hardware), and released a new version of Android TV OS, in September 2021, to partially mitigate the attack.
Videos showing the attack in action can be found at the following URL:
Spook: The Unfriendly Ghost Remote. https://sites.google.com/view/friendly-ghost-remote, 2022.
