Online Program Focuses on Cyber-Vulnerability and Risk
Purdue Online Engineering’s Design for Security badge program prepares professional engineers to better understand and identify areas of product cyber-vulnerability and risk. The courses are designed and taught by an interdisciplinary group of Purdue faculty affiliated with Purdue’s Center for Education and Research in Information Assurance and Security (CERIAS), a global leader in research and education in areas of cyber security crucial to the protection of critical systems and infrastructure.
The courses are designed and taught by an interdisciplinary group of Purdue faculty affiliated with Purdue’s Center for Education and Research in Information Assurance and Security (CERIAS), a global leader in research and education in areas of cyber security crucial to the protection of critical systems and infrastructure.
The online Design for Security program emphasizes secure design principles throughout the product development life cycle and aligns with the joint cyber security recommendations of the Association for Computing Machinery and the Institute of Electrical and Electronics Engineers. Its focus also allies with the theme of Artificial Intelligence, one of four key areas highlighted during Purdue’s Great Leaps 150th anniversary celebration.
Many emerging product technologies and services include connectivity components that are cyber-enabled (Cloud, Big Data, Mobile, Internet of Things, and Artificial Intelligence). The technologies and services help businesses add features to their products and facilitate efficiencies to better serve customers, but the inter connectivity carries with it increased vulnerability and risk.
The Design for Security badge is open to students in all STEM disciplines, but is designed specifically for working engineers and students with an awareness of secure design. The curriculum focuses both on the production level – companies that produce cyber or cyber-physical systems and their components – and the engineers and scientists who design the cyber or cyber-physical systems and associated processes.
“In response to the global increase in cyber attacks, companies are hiring a greater number of cyber security specialists, but they are also still hiring engineers and managers for traditional roles, including product development and user-interface technology,” says Joel Rasmus, managing director of CERIAS. “The Design for Security program will give these employees an understanding of cyber vulnerabilities and risks, and help them to design more secure products and services.”
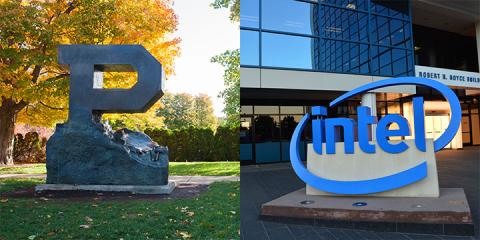
Course material introduces security principles from the physical secure design of the infrastructure to the security of the hardware and software that underlie the infrastructure, and then to the technical constraints and processes in place to support more operational security. The curriculum is offered in collaboration with the Intel Corporation and Purdue’s School of Industrial Engineering, School of Electrical and Computer Engineering and the Department of Computer Information Technology. Course content includes:
- Foundations of Secure Development, which introduces the need for secure software development, as well as the basics of security, privacy, authentication (including biometrics) and cryptography, which can help informed application designs.
- Secure Design Life Cycle, which introduces a process to build an application from its inception to its decommission, including the architecture design, development, testing, and the evaluation metric.
- Secure Operations, which introduces the principles of effective security operations, and includes the concepts of monitoring, incidence response, forensics, ethics, and legal considerations, product end of life and disposal.
- Security Applications, which introduces different example applications of secure designs like databases, web security, apps, cloud computing, machine learning, autonomous vehicles, and blockchain.
Design for Security curriculum also covers subjects including database security, network security, IoT security, cloud security, autonomous system security and block chain security.
“You can be a fantastic product developer, but if your product puts your company or customers at risk, how good is your product?,” Rasmus says. “Purdue’s online Design for Security program will help you better design and develop more secure products and services.”
Writer - Linda Carrick Thomas, Featured Word Inc