Research Vision
We wish to build a world where people can reasonably trust computing and cyber-physical systems despite the occurrence of unanticipated natural faults or maliciously induced faults. In achieving this, we believe in the power of solid technical ideas, practical techniques that can instantiate these ideas, and rigorous experimentation to prove or disprove the ideas. In the end, good ideas, and not glitzy sales pitches, win the battle for brains and minds.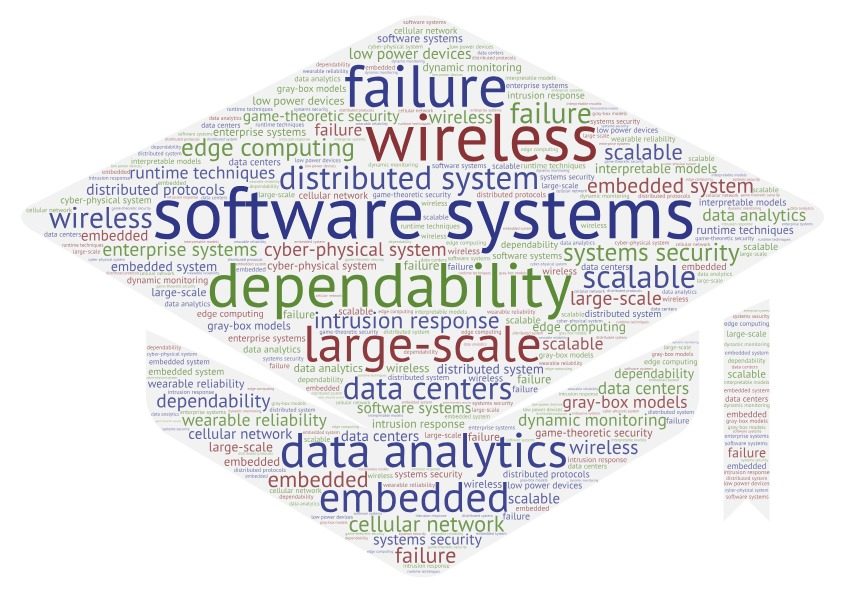
What We Do
Dependability meets Data Analytics
The broad goal of our research is to design practical dependable distributed systems. We work in the realm of systems that generate and consume lots of data and that work at large scales. Therefore, we adapt and apply Machine Learning techniques to our systems problems. Our work is motivated by the fact that systems are increasing in scale, both in terms of the number of executing elements and the amount of data that they need to process and existing dependability techniques are increasingly failing to meet the demands of such scaling. The faults that bedevil such systems may be due to accidental (or natural) causes, or malicious (or induced) causes and we deal with both classes.
Our work deals with faults by providing the functionality of detection (tell quickly that there is something wrong), diagnosis (what is the root cause of the failure), containment (how to prevent the failure from propagating through the system), and in some cases, prediction (of an impending failure, so that proactive mitigation actions can be triggered). The dependability mechanisms must not overly impact the application or the execution environment, either in terms of performance impact or in terms of the level of changes required from them. We need to use leading-edge data analytic techniques to create systems that perform these functions in an adaptive manner, adapting to the different applications, system conditions, faults and security attacks, and requirements. Our work focuses primarily in the application and in the middleware software layers, while with embedded wireless devices, we also delve into the low-level firmware.