Publications
Resilient Cyberinfrastructure
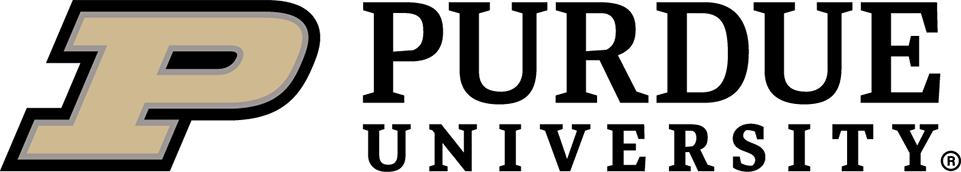
Malik, Raghav, Vidush Singhal, Benjamin Gottfried, and Milind Kulkarni. "Vectorized secure evaluation of decision forests." In Proceedings of the 42nd ACM SIGPLAN International Conference on Programming Language Design and Implementation (PLDI), pp. 1049-1063. 2021.
As the demand for machine learning-based inference increases in tandem with concerns about privacy, there is a growing recognition of the need for secure machine learning, in which secret models can be used to classify private data without the model or data being leaked. Fully Homomorphic Encryption (FHE) allows arbitrary computation to be done over encrypted data, providing an attractive approach to providing such secure inference... In this paper we present COPSE, the first system that exploits ciphertext packing to perform decision-forest inference.
Resilient Cyber-Physical Systems
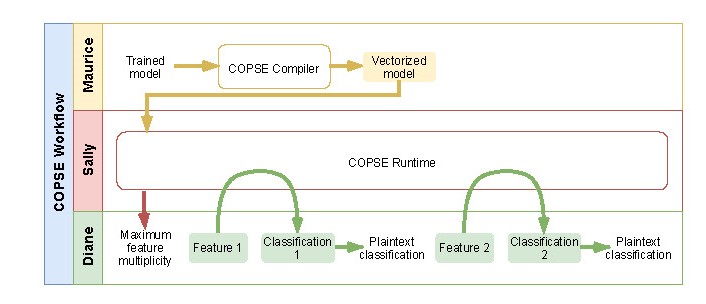
Wang, Sihan, Guan-Hua Tu, Xinyu Lei, Tian Xie, Chi-Yu Li, Po-Yi Chou, Fucheng Hsieh, Yiwen Hu, Li Xiao, and Chunyi Peng. "Insecurity of operational cellular IoT service: new vulnerabilities, attacks, and countermeasures." In Proceedings of the 27th Annual International Conference on Mobile Computing and Networking (Mobicom), pp. 437-450. 2021.
More than 150 cellular networks worldwide have rolled out massive IoT services such as smart metering and environmental monitoring... We discover five vulnerabilities spanning cellular standard design defects, network operation slips, and IoT device implementation flaws... Threateningly, they allow an adversary to remotely identify IP addresses and phone numbers assigned to cellular IoT devices and launch data/text spamming attacks against them.
Resilient Socio-Technical Systems
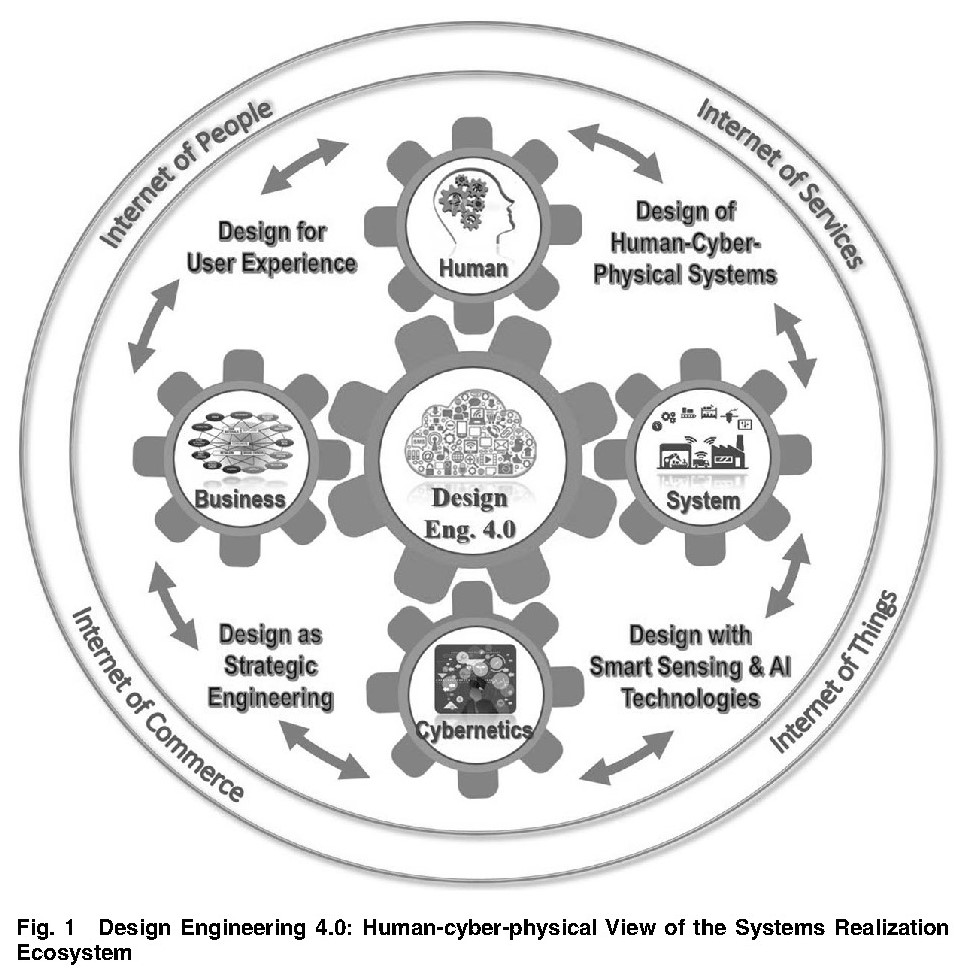
Jiao, Roger, Sesh Commuri, Jitesh Panchal, Jelena Milisavljevic-Syed, Janet K. Allen, Farrokh Mistree, and Dirk Schaefer. "Design Engineering in the Age of Industry 4.0." Journal of Mechanical Design 143, no. 7 (2021): 070801.
Industry 4.0 is based on the digitization of manufacturing industries and has raised the prospect for substantial improvements in productivity, quality, and customer satisfaction... In this paper we envision a “human-cyber-physical view of the systems realization ecosystem,” termed “Design Engineering 4.0 (DE4.0),” to reconceptualize how cyber and physical technologies can be seamlessly integrated.